CISO • RISK
Risk Score
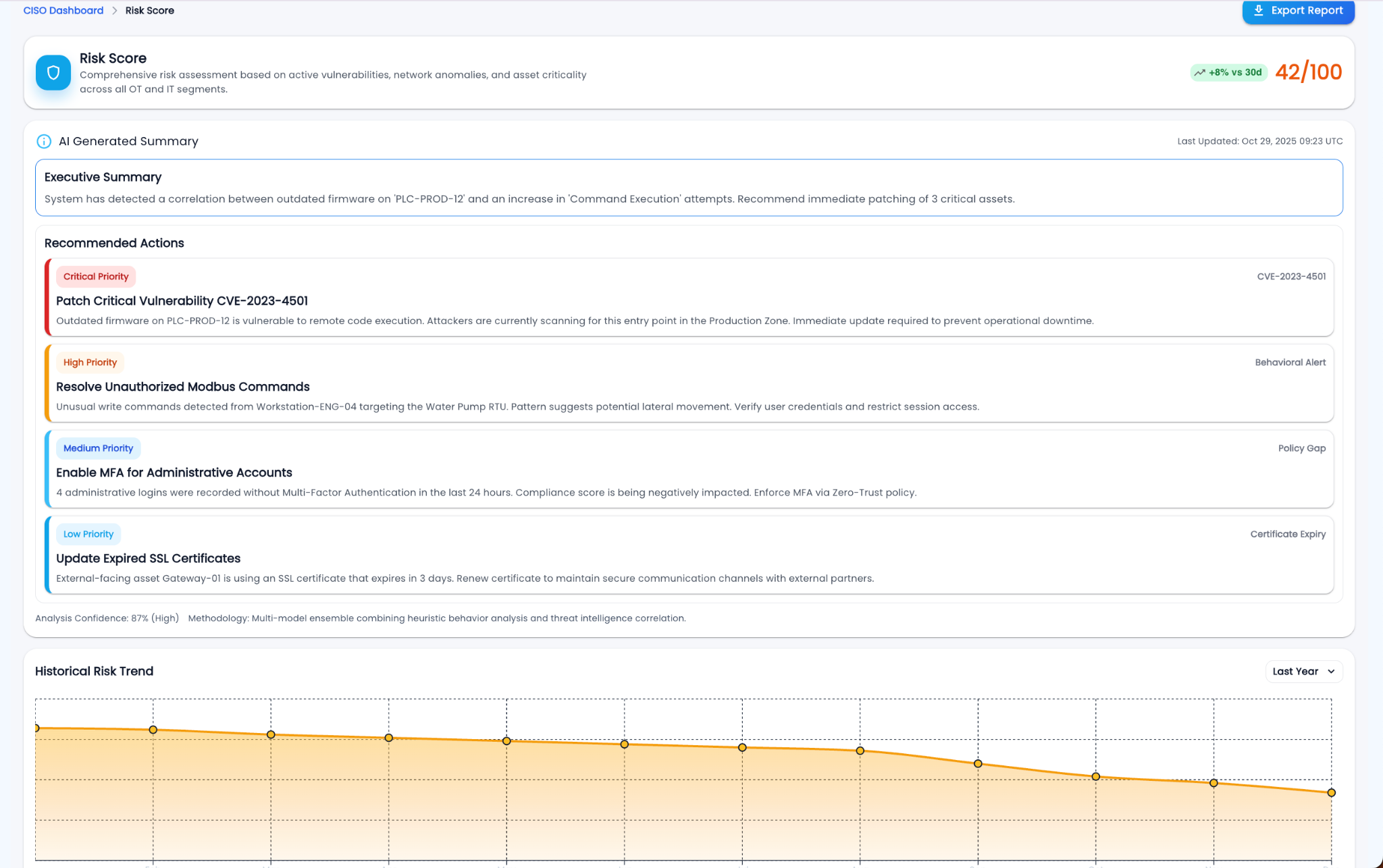
A consolidated risk assessment across vulnerabilities, anomalous behaviors, and asset criticality—normalized into a single executive metric.
What it shows
Risk Score compresses multiple technical dimensions into one number so leaders can track whether security posture is improving or drifting. It highlights *what is driving risk now*—so you can fund, assign, and verify mitigation quickly.
How it’s calculated
- Asset Criticality weighting (crown‑jewel OT/IT assets raise impact).
- Vulnerability exposure (known CVEs, exploitability, patch age).
- Behavior anomalies (protocol misuse, unusual access, lateral movement signals).
- Control effectiveness (MFA coverage, segmentation enforcement, secure boot attestation coverage).
- Recency and trend (recent spikes carry more weight than historical noise).
What to do next
- 1Open the AI Summaryand validate the top correlation (e.g., a vulnerable PLC tied to “Command Execution”).
- 2Patch or isolatethe top critical assets contributing to score increases (OT maintenance window friendly).
- 3Harden access(MFA, privileged access review, key rotation) where risk is identity-driven.
- 4Track trend weeklyand report “risk driver removed” outcomes to leadership.
KPIs to watch
Current score
/100
30‑day delta
↑ / ↓
Top driver
CVE / anomaly
Why this matters to a CISO
AI only works if it’s trustworthy
If models drift or confidence drops, you’re flying blind. This keeps the AI layer honest.
Drift is normal in OT
New firmware, new shifts, new processes—all cause drift. You need to detect it early before it erodes detection quality.
Confidence drives automation
You can’t let AI auto-contain based on shaky confidence. This metric ensures automation stays aligned with risk appetite.
Feedback loops improve accuracy
Every analyst decision sharpens the models. This closes the loop between human intelligence and machine learning.
Reference UI Screenshot