CISO • INTEGRITY
Trust Provenance (DAG)
Shows chain‑of‑custody for identities, devices, policies, and security events using a DAG-linked integrity model.
What it shows
Trust Provenance provides cryptographic traceability: how a device was onboarded, which policies were applied, and how each security decision links to prior verified states. This reduces “who changed what” ambiguity during incidents and audits.
How it’s calculated
- Each identity/device state transition is recorded as an event with signed metadata.
- Events form a DAG: new events reference previous verified events (tamper-evident lineage).
- Anchoring to an immutable ledger provides timestamping and non-repudiation.
- Policy decisions include evidence pointers (signals used, risk score, enforcement action).
What to do next
- 1Use provenance during investigations: trace the exact sequence leading to a denial/quarantine.
- 2Prove compliance: show auditors immutable evidence that controls were enforced at time-of-event.
- 3Validate onboardingfor new OT/IoT fleets: ensure each device has a hardware-bound identity.
- 4Detect tampering: flag breaks in lineage, replay attempts, or out-of-order events.
KPIs to watch
Provenance score
%
Events anchored
count/day
Lineage breaks
0 target
Why this matters to a CISO
AI only works if it’s trustworthy
If models drift or confidence drops, you’re flying blind. This keeps the AI layer honest.
Drift is normal in OT
New firmware, new shifts, new processes—all cause drift. You need to detect it early before it erodes detection quality.
Confidence drives automation
You can’t let AI auto-contain based on shaky confidence. This metric ensures automation stays aligned with risk appetite.
Feedback loops improve accuracy
Every analyst decision sharpens the models. This closes the loop between human intelligence and machine learning.
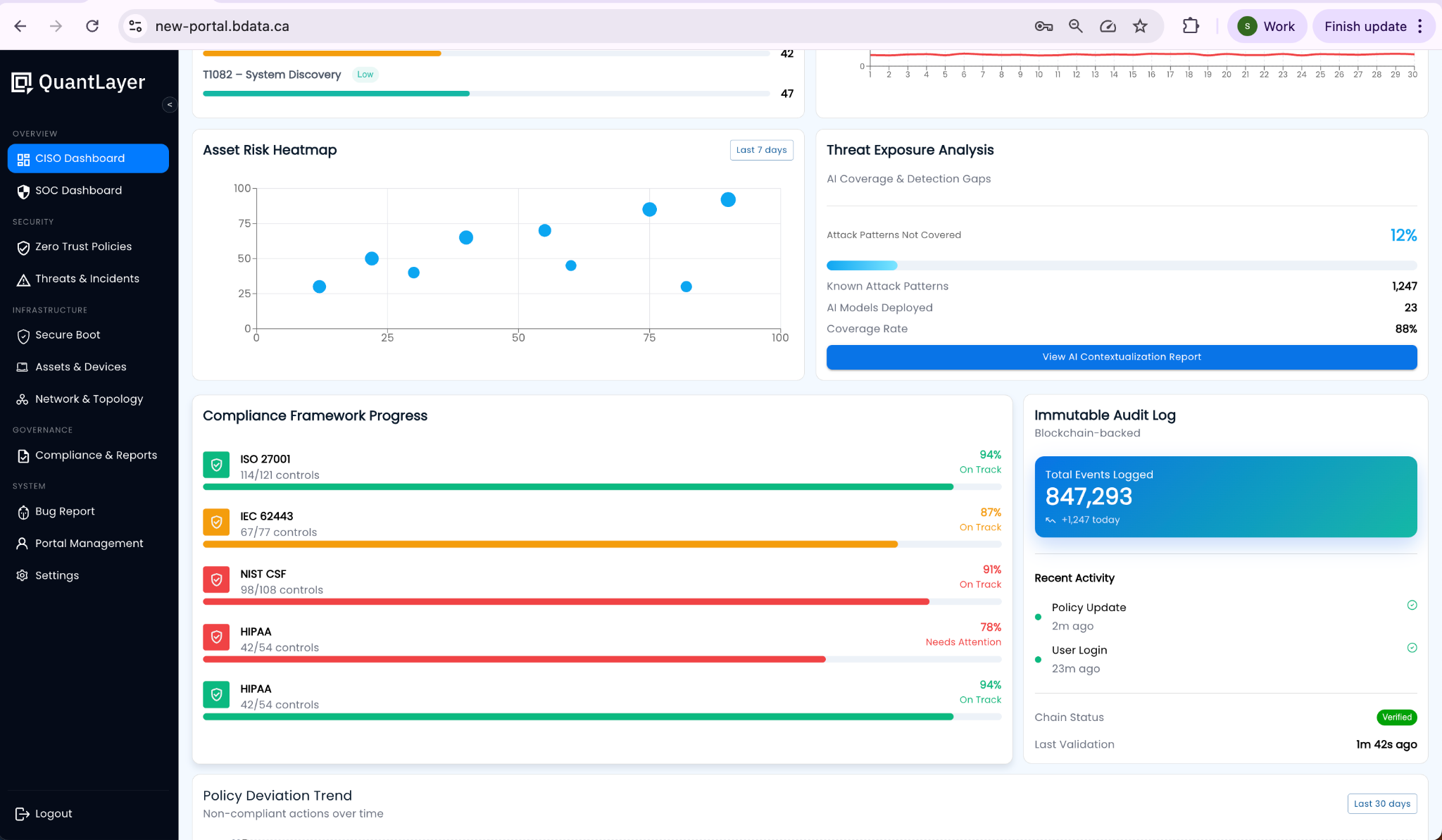
Reference UI Screenshot