Industrial Protocol Support (50+)
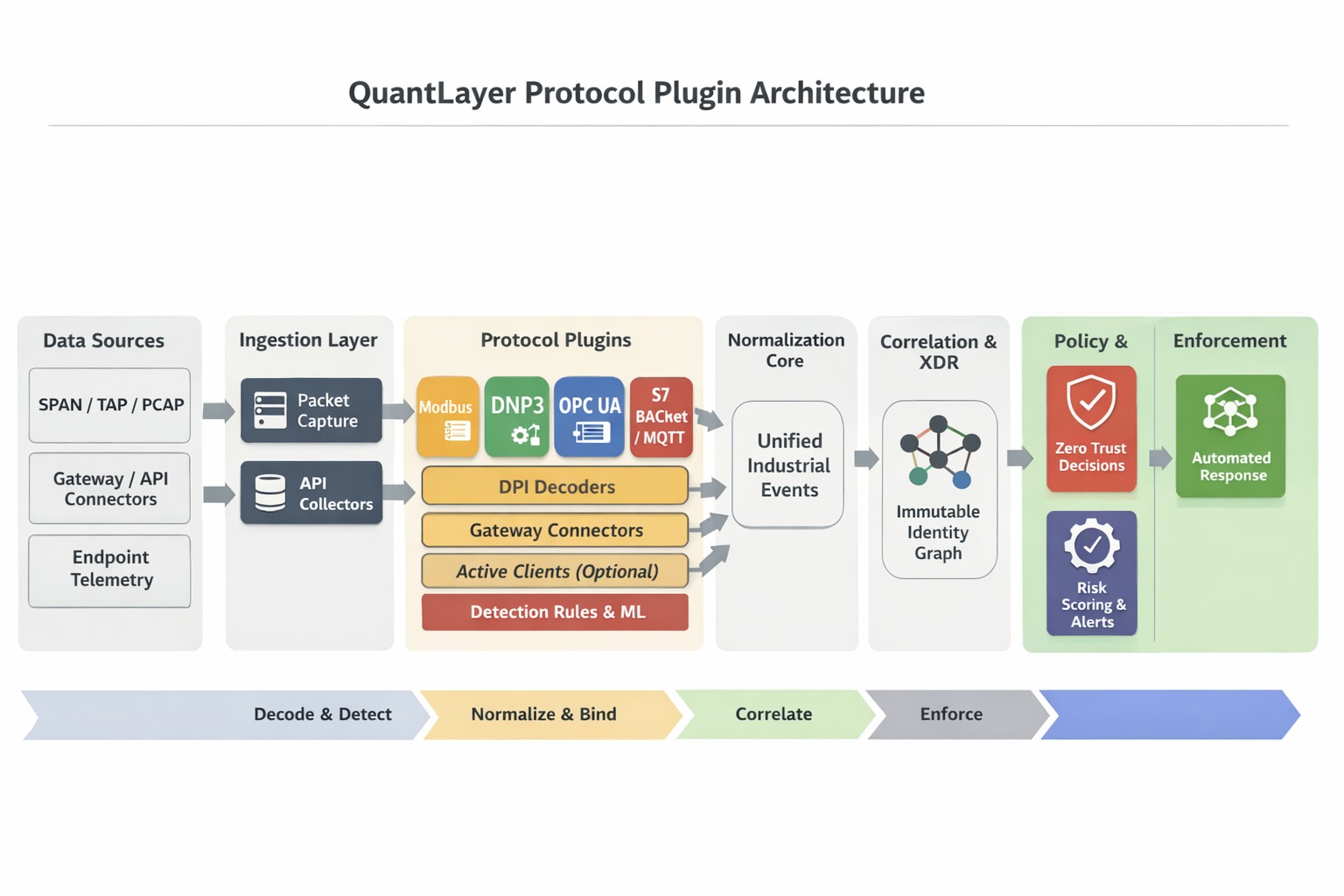
Decode intent, bind sessions to immutable machine identity, and enforce Zero Trust responses across every supported industrial protocol.
Overview
In OT environments, “protocol support” must mean more than recognizing a port number. QuantLayer XDR treats industrial protocols as enforceable states: each session is mapped to an immutable machine identity, evaluated against control policies, and continuously verified with behavioral signals.
What “supported” means in QuantLayer
How QuantLayer supports industrial protocols
Each protocol is supported through four QuantLayer layers:
Stateful parsing discovers PLCs, RTUs, HMIs, and gateways so every session can be bound to a deterministic machine fingerprint and dependency graph.
Apply identity-aware rules, anomaly detection, microsegments, and safe responses tailored to the risk appetite of each zone.
Decode protocol commands, correlate them with host/process telemetry, and feed every signal into the XDR data lake for alerts and context.
Respond to abnormal requests with adaptive policy actions, change-window guards, and requester confirmation flows without touching endpoints.
OT-safe collection
QuantLayer ingests industrial traffic through passive taps, SPAN/mirror ports, inline observers, and agentless middleware so collection never disrupts production.
- Zero-footprint sensors plug into mirrored segments for CIP, Modbus, DNP3, and other real-time protocols.
- Gateway connectors (OPC UA, MQTT, MQTT-SN) bring downsampled telemetry into the QuantLayer mesh while honor change windows.
Supported protocol list (50+)
Below is a clean list of industrial protocols QuantLayer XDR can support, grouped by common OT/ICS domains.
Modbus TCP Modbus RTU (via gateway) EtherNet/IP (CIP) PROFINET PROFIBUS DP Siemens S7 (S7-300/1200) Mitsubishi MELSEC Omron FINS Rockwell DF1 EtherCAT OPC UA (via gateway)
DNP3 DNP3 Secure Authentication IEC 60870-5-101 IEC 60870-5-104 IEC 61850 MMS IEC 61850 GOOSE IEC 61850 Sampled Values IEC 61850-9-2LE IEC 62056 (DLMS/COSEM) IEC 62351 ICCP/TASE.2 OPC UA PubSub
HART (via gateway) WirelessHART FOUNDATION Fieldbus ISA100.11a Modbus Plus PROFIBUS PA ControlNet DeviceNet AS-i CIP Safety
BACnet/IP BACnet MSTP (via gateway) KNX/IP KNX TP (via gateway) DALI (via gateway) LonWorks/IP OPC UA Web services for building systems
MQTT MQTT-SN AMQP CoAP LwM2M DDS OPC UA PubSub WebSockets/HTTP APIs LoRaWAN IEEE 802.15.4
SSH RDP VNC TLS/HTTPS (secure APIs) Mutual TLS IPsec/VPN tunnels SFTP/SCP SNMP/NTP monitoring
Note on vendor/proprietary stacks
Where vendor protocols are proprietary, tunneled, or carried over OEM management planes, QuantLayer still observes intent through gateway connectors, engineering tools, and enriched telemetry so high-level assets remain enforceable and auditable.
Protocol-aware detections (examples)
- Unauthorized writes (register/tag/parameter changes outside approved change windows).
- New master/controller initiating remote commands (rogue engineering station or unmanaged gateway).
- Unsafe command sequences that deviate from established process order or safety interlocks.
- Protocol tunneling, abnormal port/protocol mismatches, or duplicated sessions.
- Lateral movement between OT zones using ICS protocols outside documented conduits.
- Identity drift when a device fingerprint no longer matches its expected role.
Policy enforcement patterns
Log every session, fingerprint, and intent without blocking so teams can baseline behavior and validate policies before staging.
Trigger deny/quarantine, microsegment, or step-up flows only when risk thresholds and change approvals align with safety windows.
Evidence & reporting
- Who/what identity participated in each session, when it began, and when it ended.
- Policy decisions tied to evidence (allow/warn/deny) along with signed telemetry.
- Change windows, approvals, and OT-safe enforcement steps captured for audits and controllers.
Compliance alignment
This approach supports industrial governance models aligned with IEC 62443, NIST SP 800-82, and sector-specific frameworks so every protocol decision is traceable and defensible.
QuantLayer XDR treats industrial protocols as enforceable sessions, combining protocol parsing, identity, policy, telemetry, and OT-safe controls.